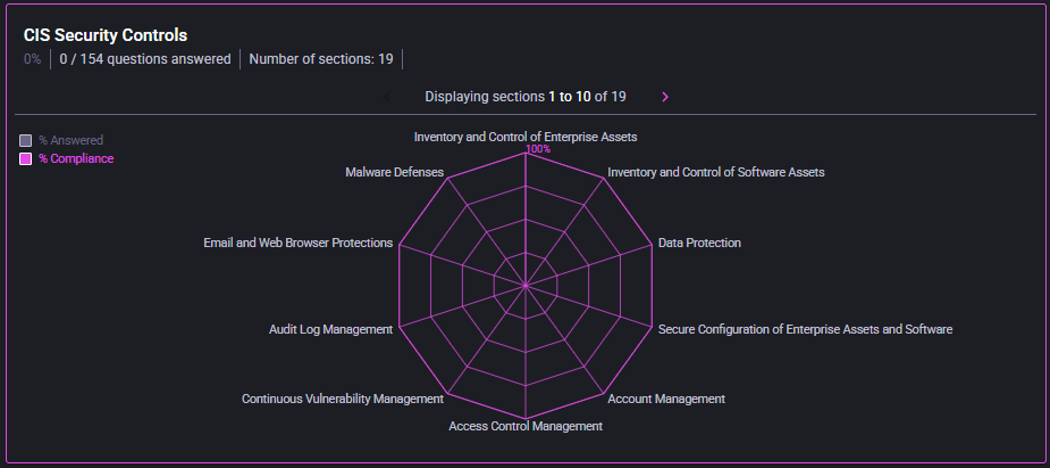
CIS Security Controls
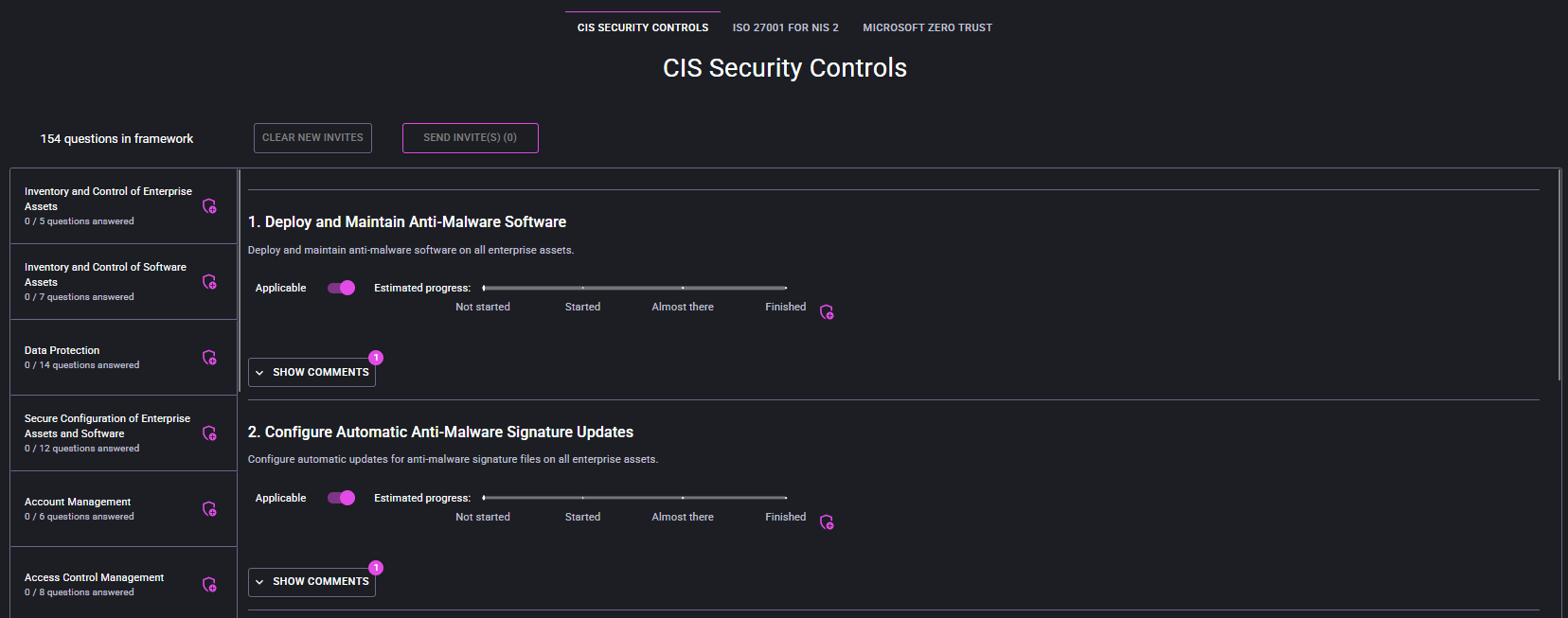
Use this framework to assess day-to-day operational control maturity across key cyber security control areas.
- % Answered: progress through questionnaire items.
- % Compliance: control compliance level for answered scope.
- Radar chart: section-by-section strengths and weak areas.
- Start with low-scoring sections from the radar chart.
- Confirm whether gaps are process, tooling, or ownership related.
- Document one action per gap with owner and due date.
Prioritized CIS remediation backlog grouped by section (quick wins, medium-term, strategic).