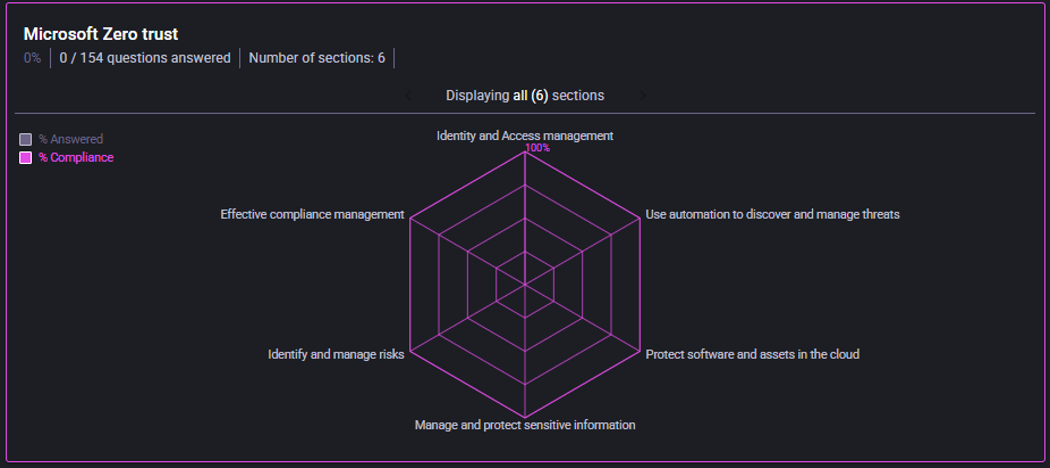
Microsoft Zero Trust
Use this framework to evaluate identity-first and cloud security posture aligned with Zero Trust principles.
- Identity and access management
- Threat discovery and automation
- Cloud asset and software protection
- Sensitive information protection
- Risk and compliance management
- Review domain scores and identify weakest domains.
- Map each weak domain to required controls/policies.
- Define cross-team dependencies (IAM, SOC, cloud ops, governance).
Zero Trust improvement plan with phased implementation priorities.